Overview
This was a group project for my Ethical Hacking course. My group of three was tasked with analyzing three embedded device firmwares and then creating a repeatable script to scan for our findings.
While all members contributed to the analysis & report, I focused more on the script and my teammates did more on the OSINT and analysis.
A high-level overview follows, see the report for more details.
The Brief
The manufactured ThanosTech LLC requested a static firmware security assessment of three firmware images used in their communication relay devices.
- TP-Link TL-WR841N Router image
- D-Link DCS-8000LH IP Camera image
- Bare-Metal ELF firmware designed to simulate an STM microcontroller
The engagement was scoped to offline static analysis and repeatable automation only, meaning no live exploitation or network testing was permitted. Our goal was to identify security risks in the firmware such as hard-coded credentials, outdated dependencies, and embedded secrets.
From these findings we were to produce a mitigation report, as well as a lightweight script written in bash or python for use in triage.
Script
Design
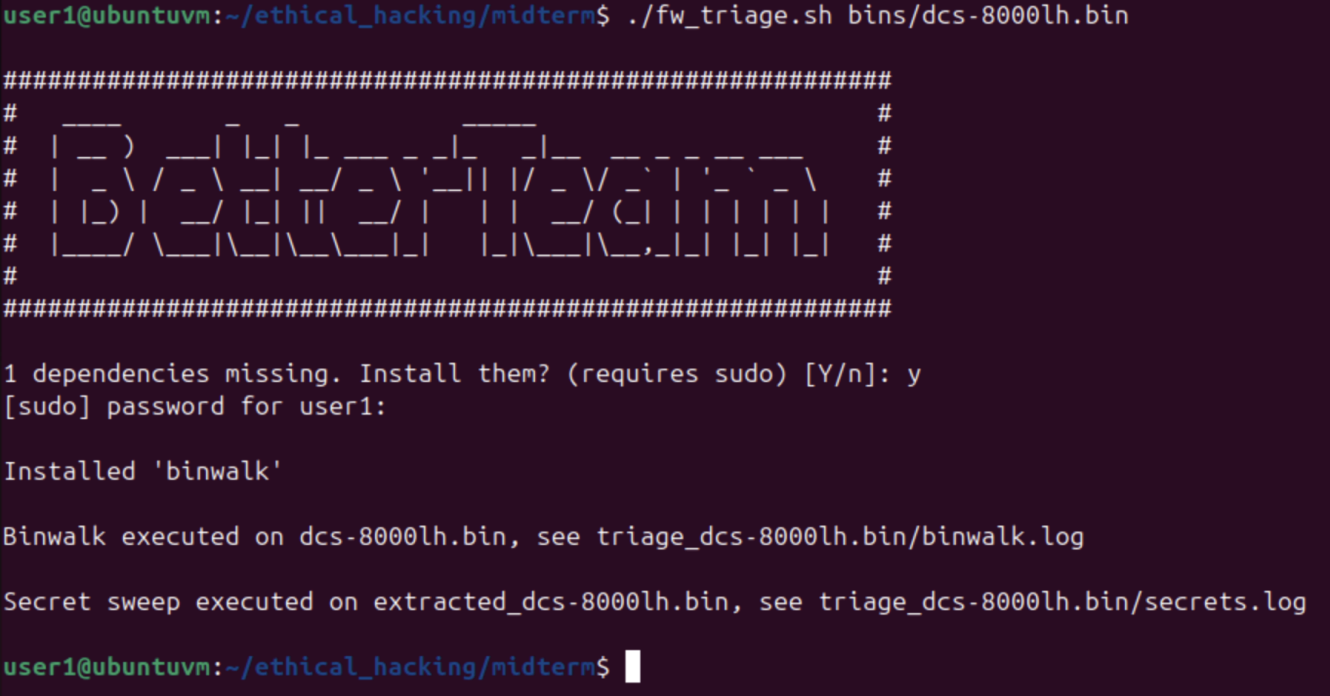
The script was written in bash with support for versions as low as 3.2.57 (the version shipped with macOS), to provide maximum portability.
Since this script is intended for triage use, it was designed in a modular fashion allowing for future expansions targeting new systems and vulnerabilities.
To achieve this goal, functionality was split into component files which each performed a specific analysis and reported their logs and findings. These components were executed by an orchestration script which determines the target type and acts accordingly.
Capabilities
- UX support with dependency verification + automatic installation, help messages, and aggregated logs.
- Extraction for ELF and binary firmwares.
- Scanning modules targeting hard-coded credentials and keys.
- Support for custom modules and dynamic execution.
Dependencies
| Tool | Usage | Desc |
|---|---|---|
file | recon | determine data formats and architectures, used to guide tool usage |
binwalk | extractor | extract binaries and compressed data, setting up for further tools |
readelf | extractor | inspect ELF metadata to guide tool usage and analysis |
objdump | extractor | produce human and tool readable content from assembly objects |
ripgrep | scanner | primary scanning tool used to identify common secret patterns |
strings | scanner | extract human readable text for analysis, focusing on version information and tags |
Findings
Hard-Coded Root Passwords
Affected: TP-Link, D-Link
Vulnerability
A startup script writes clear-text credentials to /var/passwd & /etc/shadow. This allows anyone with the ability to read the firmware root access to the device during operation.
Mitigation on Avoid hard-coded passwords. Replace with randomized generation, secure provisioning, or public/private encryption.
Embedded Private Keys & Credentials
Affected: Bare-Metal ELF, D-Link
Vulnerability
Private Keys, AWS Credentials, and GitHub auth tokens stored insecurely in firmware. This provides an attacker access to services beyond the vulnerable device, allowing breach of or exfiltration from cloud services.
Mitigation
Store secrets in a secure hardware device (e.g. TPM). Provision unique device keys with scoped access and lifetimes instead of static credentials.
Outdated BusyBox
Affected: D-Link, TP-Link
Vulnerability An outdated BusyBox version with known and reported exploits in use on both devices.
Mitigations
- Upgrade to a patched version when available, disable or harden vulnerable applets until then.
- Switch to a more secure dependency with no known vulnerabilities to cover BusyBox’s use case.
Insecure Boot Chain
Affected: D-Link
Vulnerability: Outdated U-boot version with known vulnerabilities, allowing execution of unsigned code. Network boot protocol that potentially allows for remote execution of these exploits.
Mitigations Upgrade U-boot version, disable network boot protocols. Enforce firmware signatures.

